Hello everyone,
what is actually the security solution or service with which providers earn the most money on the bottom line?
Firewalls.
Here are the figures of the relevant manufacturers for which the operating profits are available (at Cisco, for example, there is no corresponding segment reporting):
Enterprise | EBIT margin (last published) Annual Financial Statements) |
|---|---|
Checkpoint | 34% |
Securepoint | 33% |
Fortinet | 31% |
Trend Micro | 21% |
Sophos | 9% |
If you compare the profit margins with Crowdstrike, Okta, Elastic or other (almost) thoroughbred security players, you will find that there are minus signs before EBIT everywhere, even with billions in sales. Nothing is as lucrative as digital firewalls.
With Fortinet et al., we can also confidently assume that the legacy firewall business has to finance the expeditions into competitive territories such as EDR/SIEM etc., so the firewall margins are significantly higher than the published figures.
One explanation could be that there is obviously less competition in firewalls for enterprise customers than in other security areas. And that none of the competitors is called Microsoft. In addition, there is the higher stickiness of access-centric security solutions vs. e.g. detection-based solutions. Access control is always embedded in business logic and workflows and is therefore by definition more difficult to replace than tools that are only used by the security team.
The worst security buyer on the planet strikes again, on the subject of renewals:
- „Successfully negotiating renewals is a lot like demanding a raise. It’s more effective when you’ll walk away. You don’t have to want to, but you need to mean it. You need to have the alternatives, the plans, and, crucially, the spiteful rage to drive you down the alternative path. If you don’t, you’ll be halfhearted, the vendor will sense it, and you won’t get very far. But if you can channel the hate, you’ll get those 90% discounts. I promise.”
- The most interesting aspect of this is that sales teams often no longer receive a commission on the previous contract volume when renewing licenses, but only on the net increase in customer sales (through additional users, modules, price increases). This means that it does not matter to sellers whether the customer threatens to renew the licenses only if the price is reduced – either way, this does not help with quota fulfillment and Take Home Pay. In the end, this commission regulation means that sales teams of the providers already used are less motivated in renewals than the competitors who may be able to win a new customer.
- The result of a current tender for an MDR service based on Defender XDR Suite fits in with this as “anecdotal evidence”: Customer with ~5000 endpoints, price reduction of 65% achieved when changing provider compared to current service (covered only EDR, i.e., lower coverage), and that with the same SLA as reaction/response/hunting.
As an interim solution of XDR and SIEM, some MSSPs now offer the combination of XDR for real-time discovery + data lakes for log analysis in suspected cases.
Data pipeline tools such as Cribl, Datadog, Databahn or Tenzir are the current tools of choice. However, Microsoft has already recognized the trend and is starting to roll out a Sentinel Data Lake, which achieves 85% cost reduction compared to log analytics storage, and still allows hunting via queries.
While Trump is restructuring CISA, the BSI’s budget is being increased by 50%. Speaking of BSI: A colleague pointed out to me that in addition to the list of qualified APT service providers, there is also a BSI list of certified service providers for the “Incident Processing Area”. An important requirement here seems to be the provision of a sufficiently large team of incident experts to enable supra-regional deployment. As of today, only 4 providers are listed: Secunet, Hisolutions, TÜV Trust IT and Deutsche Telekom. I assume that the list will continue to grow as it becomes better known.
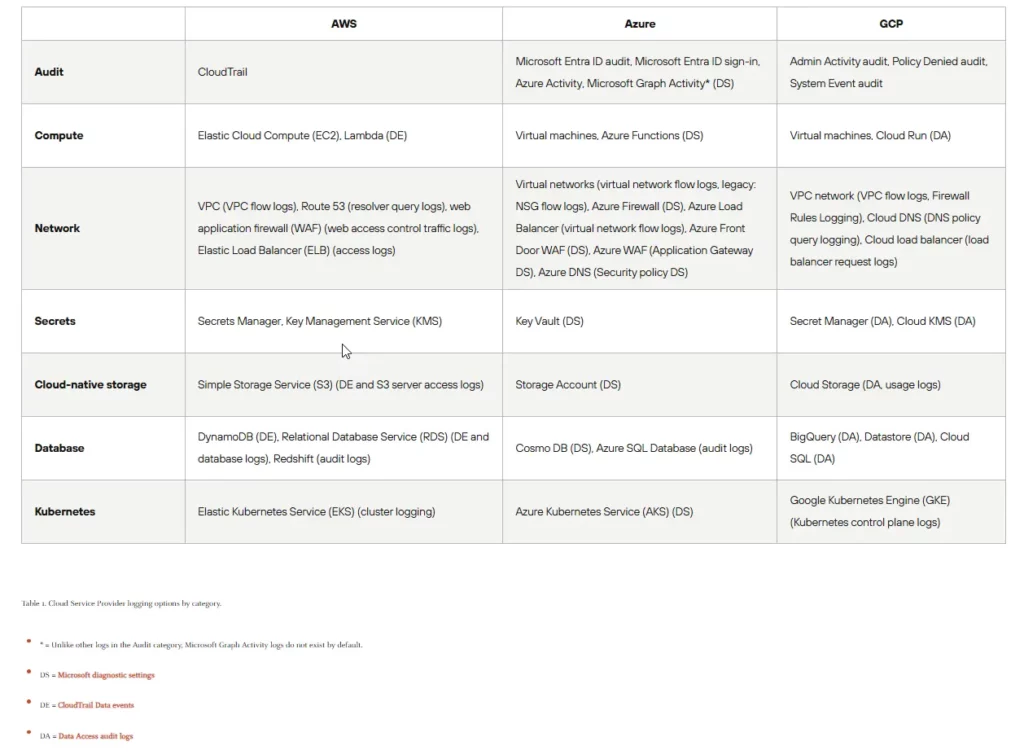
Fani Akbar (AWS Pen Test Crack) has dealt with AWS log sources (Cloudtrail, VPC Flow, Guardduty…) as part of a recent comprehensive red teaming, sorted them in order of importance and also included some detection (real time and UEBA) + response rules (such as deactivation user). Written in a very understandable way. S3 Access Logs and Eventbridge tended to be unimportant. The approach of evaluating the effectiveness of the detection rules is also exciting: by combining trend analysis of true and false positive rates as well as targeting synthetic data that contains attack techniques (i.e. a library of logs with hidden IoA / IoC, so to speak). DORA regulated customers are familiar with the problem that the effectiveness of the detection rules must be verifiable. On a slightly higher flight level, the Palo Alto Unit42 has created a very good overview of cloud log sources on control and data layers (see attached).
Digital sovereignty: The European cloud providers refer loudly indignantly to an interrogation before the French parliament, in which Microsoft’s foreign minister admitted that the US government could also gain access to customer data in the “European Sovereign Cloud”. Keywords Cloud Act, Patriot Act. In my opinion, this problem can be solved by customer-specific encryption. Much more questionable is the dependency on operation as long as the source code is unknown, isn’t it?
But to be honest, I prefer to transfer my protection money to Microsoft on the first of the month rather than to Moscow. In the whole debate, dependence on mobile devices is also avoided. Who else but the Federal Chancellor uses a telephone with European hardware and software? And if you read the business news in the newspaper, you will probably notice that board members in the DACH region are busy with problems such as slumps in sales, profit warnings and job cuts across the board – very specifically in the here and now. There is little financial leeway for dealing with theoretical risks. Most companies will probably only opt for digitally self-sufficient solutions if this is either possible at no additional cost or required by law.
Are we running into security saturation? Simply surfing the wave is definitely not enough (anymore). Less than half of all security providers grew at all in the first half of 2025, reports IT Harvest. And the latest IBM Data Breach Report hides an interesting figure: For the first time, less than half of all organizations that have been victims of an attack (“breach”) have subsequently increased their security budget. This can only mean that the majority of victims have assessed further investments in security as unprofitable despite the incident. The report also quantitatively evaluates security measures according to risk reduction. According to the survey, top 1 is DevSecOps, top 2 is “AI driven insights”, top 3 is a SIEM. Having a CISO at all ranks 20th out of 21 😉.
On the other hand, there is no saturation when it comes to money on the financing side: In the first half of 2025, funding for security companies rose to around USD 10 billion, which is about 20% more than in the previous year. #UnstoppableBullMarket.
Concrete news from the M&A department:
- The big headline, of course, is Palo Alto‘s acquisition of CyberArk:
- For 25 billion USD, which is about 20 times the turnover, factor 80-100 on free cash flow and about 25% premium on the share price before offering
- No deal for value investors: CyberArk is still not profitable (see above), among other things, ~48% of sales are spent on sales+marketing
- With 10,000 customers, 4,000 employees, ~30% revenue growth and one of the leading IAM/IGA/SSO/PAM/NHI solutions, this is a strong addition to the platform that PAN aims to offer. Integration will be a Herkules and Fraukules task!
- Before that, there were rumors of a takeover of SentinelOne by PAN, which briefly helped S1’s share price turn around. By the way, IDC estimates the market share in the EDR market among enterprise customers as follows: Microsoft ~25%, Crowdstrike ~18%, SentinelOne ~10%, Palo Alto ~5% and the rest is distributed among Trend Micro, Sophos, Broadcom etc.
- The Italian arms company Leonardo buys
- 25% of SSH Communications (PAM solution from Finland, founded 30 years ago by the inventor of the SSH protocol). SSH is valued at ~EUR 100 million in total – with a turnover of around EUR 20 million and with a changing sign for profit.
- And Axiomatics, a Swedish provider of context-based access control
- LevelBlue (MSSP from the USA, subsidiary of AT&T) is still on a shopping spree – after the cybersecurity consulting of AON, Trustwave has now been acquired. Trustwave is also an MDR provider and had ambitions to buy Cybereason about 1 year ago. However, the merger was then cancelled.
- Axonius (vulnerability management) buys Cynerio (OT/MIoT NIDS with focus on healthcare, similar to Asimily)
- Vanta (GRC) raises another $150 million in funding, at a valuation of ~$4 billion
Notes from vendor conversations:
Defenderbox:
- German startup, funding from NRW, already 50 customers (from SMEs with 25 employees to banks)
- Combines Nessus Scans + Horizon3 Pen testing from the inside and outside, as well as darknet searches for compromised credentials
- Deploy in-house via physical or virtual appliance
- Of course, everything is fully automated (weekly intervals), as a managed service with prioritized recommendations for action
- Add-on modules such as AD Audit (Purple Knight)
- Price from 500 EUR/month
Maze:
- UK startup for automatic vulnerability prioritization
- Cool approach: AI trained by security specialists in the risk analysis of vulnerabilities. Too bad I didn’t have the idea! Actually, obviously, and a problem that all organizations have
- No agent installation, and no own scanner, but use the scan results of Tenable or similar.
- Assesses impact and prerequisites of exploitability (e.g., whether vulnerable software components are loaded at all) by theoretically testing the attack vectors => ~98% reduction in vulnerabilities to be fixed
- In the demo, an example was that the AWS Nitro hypervisor prevents the exploitation of a Linux kernel vulnerability because there is no virtual USB port, and therefore the fix can be deprioritized.
- In another case, the WAF (of course) had exceptions for internal IP addresses that can be spoofed => exploitable, high risk of exfiltration of sensitive data
- So far only for IaaS systems
- AWS Bedrock Hosting in EU Tenant => Customer Data Is Not Shared with LLM Providers
- Founder was previously head of development at Tessian (sold to Proofpoint )
- Early stage, no paying customers yet
Ultrared:
- CTEM platform from Israel, bootstrapped, profitable
- Interestingly, according to the founder (already his 2nd security startup), it is much easier to win enterprise customers in Japan than in the EU or the USA. The marketing craze in Japan is probably not yet so pronounced
- ~100 enterprise customers (end users + MSSP), also in the EU
- Agentless, outside-in scans for asset & vulnerability discovery. So it’s in full competition with about 30 other solutions in the category, from Tenable to Bitsight to Cymulate (and of course now XBOW)
- Focus on keeping false positives as small as possible by means of safe PoC exploits. The validation is displayed transparently and can thus be checked
- Graphical representation of the connected assets
- AI Wizard for generating SIEM rules based on vulnerabilities found
- Still looking for channel partners for the DACH region (distributor Aqaio)
As always: Questions, suggestions, comments, experience reports, topic requests and also opposing opinions or corrections are welcome by email. Ditto for unsubscribing from the mailing list.
For the people who have received the market commentary for the first time: Here you can register if you are interested or siphon off the archive for AI training purposes.
Regards
Jannis Stemmann






